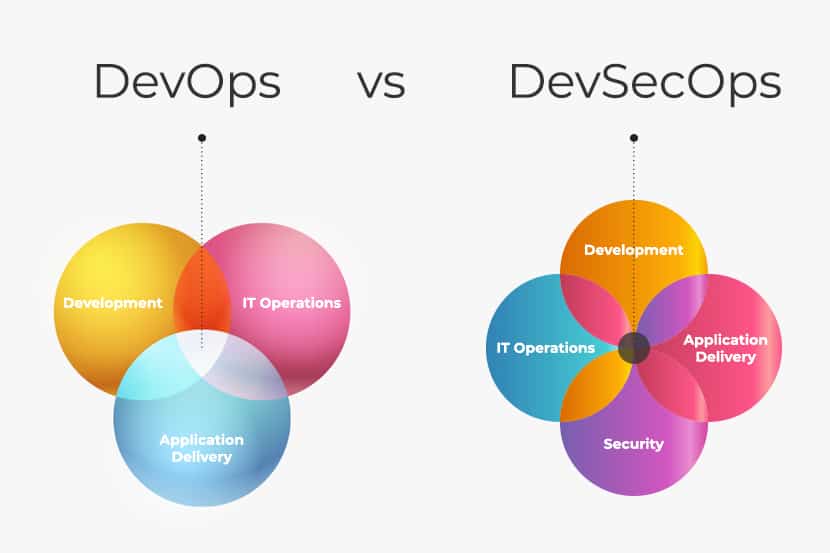
Today’s businesses seek to incorporate DevSecOps into their developmental and operational processes. Security DevOps allows you to incorporate security inability to monitor and detect attacks controls into your software and infrastructure without compromising on agility.
Many companies may have trouble preventing security risks. Generally, it is because of their inability to monitor and detect attacks. Reliable cloud security providers such as https://sonraisecurity.com/who-we-serve/devsecops/ aid you in choosing the right solutions for DevSecOps.
The main domains of DevSecOps enhance your ability to better control and security. Read on to know about these domains and how they can help your workflow.
Development Security
The development security domain deals with your product’s technology and design. While developing your software, any errors in its technology, design and implementation lead to a poor outcome. Additionally, it causes security vulnerabilities as well.
By improving your software quality, you can ensure better security. The development security domain aims to develop your software by meeting security goals and protocols.
To improve development security, you can consider the following at different stages:
Planning Stage
Planning stages involve documenting the ideas of the software you are seeking to develop. It is essential to identify and document the tasks that can support security functions and features. It can be encryptions or building tests.
You can then equip your task backlogs with crucial security measures. Additionally, make sure to perform threat modeling to gain better control over your development security.
Implementation Stage
The security functionality and features that you identify in the planning stage are beneficial in the implementation stage. Such security objectives allow you to reduce any bugs within your codes.
If any bugs are left in your code, attackers can exploit them. Your entire team has to be aware of safe coding practices. The codes can then automatically enforce through integrating tests.
Pipeline Security
The pipeline security domain utilizes crucial tools to automate steps from your source code towards production deployment. It makes sure that the deployment and build of automation toolchains support security.
This domain includes the following subdomains:
Continuous Integration (CI) Process Security
CI involves hosting your source codes repository. You can make changes to it numerous times during the day. Once you merge a change, it automatically compiles and tests the build.
During the merging phase, you can detect bugs with the help of branch policies and code reviews. You can then test the build with SAST (Static Application Security Testing) tools. It allows you to discover any vulnerabilities and errors in the programming.
Such automated testing verifies and strengthens your security baseline. It helps you to retain control over the entire process.
Continuous Delivery (CD) Process Security
CD undertakes the procedures of packaging and deploying your product. Each version of your product automatically deploys to production. The process is often called continuous deployment.
It is essential to verify and protect your build artifacts by signing them. These are stored in a secured registry. Later, you have to conduct deployment security tests to verify if the deployment is successful.
Ensure that the network configurations, security groups, and encryption keys are the ones you expect. Additionally, check if your logging pipelines are effectively capturing and storing the deployed events.
Production Security
The production security domain handles your product’s security aspects when deployed. Additionally, it deals with development tools as well. The domain utilizes the combination of security detection, response, and prevention elements.
It aims to create a resilient and stable area for production. The domain prevents any breaches from attackers into your data and pipeline. It involves the following:
Securing Your Platforms
You can secure your platforms by a process called hardening. It uses various practical security settings to harden your codes and other workloads. It can minimize surface attacks.
Production security also calls for backing up essential data. Make sure to have a solid backup policy in place. Additionally, ensure not to overlook security updates. These updates are crucial to steer clear of vulnerabilities.
It is also essential to secure the access of your administrators and operators. This step stabilizes your operational security.
Testing and Monitoring
Apart from automatic security testing, it is recommended to practice manual testing. You can utilize exploratory testing such as bug bounties and penetration tests.
Proper and regular monitoring is also crucial. It provides you better visibility and control. Security threats will not remain unnoticed. You can work on resolving them before any significant damage.
Response
It is essential to plan and rehearse your response process. Make sure to establish the roles, escalation procedures, and methodologies in advance.
A controlled and quick response to security threats can safeguard your productivity. Moreover, it also saves costs and time.
The domains of DevSecOps ensure that you possess adequate control and security. Make sure to understand and implement the best security measures within each domain. It helps to boost your productivity.